Collision Handling Technique – Open Addressing
Imagine a classroom with fixed chairs. A student comes in. His seat number is 7. But seat 7 is already occupied. Now what?
In Separate Chaining, we add another chair beside it.
But in Open Addressing, we do something different. We say – “Find another empty seat inside the same classroom.” That is the core idea of Open Addressing in hashing.
Today, we will understand Open Addressing clearly – its types, algorithms, examples, time complexity, space complexity, and real applications. If you are preparing for GATE, UGC NET, placements, or interviews, this topic is extremely important.
.
What is Open Addressing?
Open Addressing is a collision handling technique in hashing where –
- All elements are stored inside the hash table array itself.
- If collision happens, we probe (search) for another empty slot using a specific probing technique.
No linked lists. No extra memory. Just smart searching. In this technique, load factor α must always be less than 1. Because once the table is full, insertion stops.
.
Types of Open Addressing
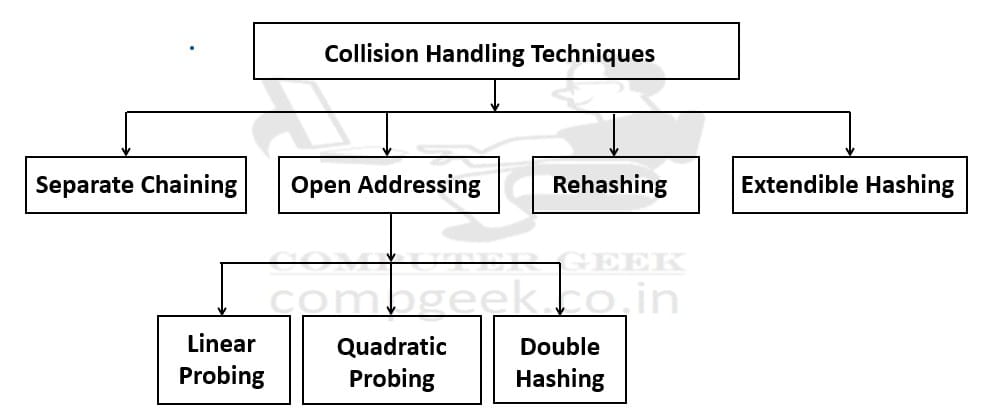
There are three main searching (probing) techniques –
- Linear Probing
- Quadratic Probing
- Double Hashing
Each one tries to solve collision in a slightly smarter way.
Linear Probing
“If collision occurs at index h(k), check the next index. If that is full, check the next. Continue until an empty slot is found.”
Simple. Straight. Like standing in a queue.
.
Algorithm – Linear Probing
Insertion –
- Compute index = h(k)
- If slot is empty, insert
- Else check (index + 1) mod m
- Repeat until empty slot found
Searching –
- Compute index = h(k)
- If key found, return
- Else check next slot
- Stop when empty slot found or key located
Example
Let m = 7 and Hash function h(k) = k mod 7
Insert keys – 10, 17, 24
10 mod 7 = 3 → index 3rd is empty → insert 10.
17 mod 7 = 3 → collision → check 4th index (empty) → insert 17
24 mod 7 = 3 → collision → check 4th index (full) → check 5th Index (empty) → insert 24
Table looks like –
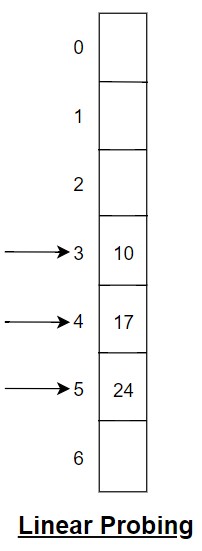
You see a cluster forming. This is called Primary Clustering.
Time Complexity – Linear Probing
- Best case – O(1)
- Average case – O(1) when α small
- Worst case – O(n)
As load factor increases, clusters grow. Performance degrades sharply.
Space Complexity – Linear Probing
The space complexity of Linear probing is O(m). There is no extra linked lists. It is only an array.
.
Quadratic Probing
“In open addressing, when collision happens, we must find another empty place inside the same hash table. In quadratic probing, we do not move step by step. We move in square steps.”
Suppose a key is hashed to index h(k), and that position is already full. Then we check –
h(k) + 1²
h(k) + 2²
h(k) + 3²
and so on (mod m)
So actually we are jumping like +1, +4, +9, +16 …
Because of this square movement, elements do not form a long continuous cluster like in linear probing. They get more space and spread better inside the table.
In simple words, quadratic probing handles collision by checking positions at increasing square distances instead of checking every next index. It reduces clustering, but it still cannot remove it completely.
.
Algorithm – Quadratic Probing
Insertion –
- Compute h(k)
- For i = 0 to m-1:
index = (h(k) + i²) mod m - Insert at first empty slot
Searching –
Same probing sequence used until key found or empty slot encountered.
- Compute index = h(k)
- If key found, return
- Else check next slot
- Stop when empty slot found or key located
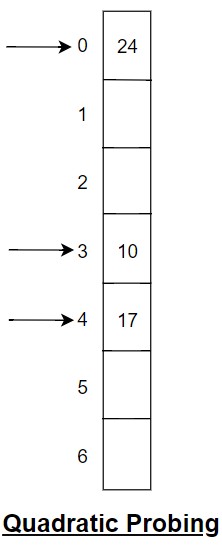
Example
Let m = 7 and H(k) = k mod 7
Insert – 10, 17, 24
10 mod 7 = 3 → index 3rd is empty → insert 10.
17 mod 7 = 3 → collision → 3 + 1² = 4 → index 4th is empty → insert 17
24 → collision → 3 + 1² = 4 (full) → 3 + 2² = 7 mod 7 = 0 → index 0th is empty → insert 24
Now keys are more spread out.
Table looks like –
Time Complexity – Quadratic Probing
- Best case – O(1)
- Average case – O(1) when α small
- Worst case – O(n)
It reduces primary clustering but still has Secondary Clustering. Keys with same initial hash follow same probe sequence
Space Complexity – Quadratic Probing
The space complexity of Quadratic probing is O(m). There is no extra linked lists. It is only an array.
.
Double Hashing
“In open addressing, when collision happens, we must search for another empty position inside the same hash table, we use one more hash function to decide how far we should jump.”
If collision happens at h1(k), then the next position is calculated as –
h1(k) + i × h2(k) (mod m) where i = 0 to m-1.
Here, h2(k) = k mod p, where p is equal to the prime number less than m.
.
So, h2(k) gives the jump value, and this jump value is different for different keys.
Because the step size depends on the key itself, keys do not follow the same probing pattern. So clustering is reduced a lot compared to linear and quadratic probing.
.
Algorithm – Double Hashing
Insertion –
- Compute h1(k)
- Compute h2(k)
- For i = 0 to m-1:
index = (h1(k) + i × h2(k)) mod m - Insert at first empty slot
Searching –
Follow same probing sequence.
- Compute index = h(k)
- If key found, return
- Else check next slot
- Stop when empty slot found or key located
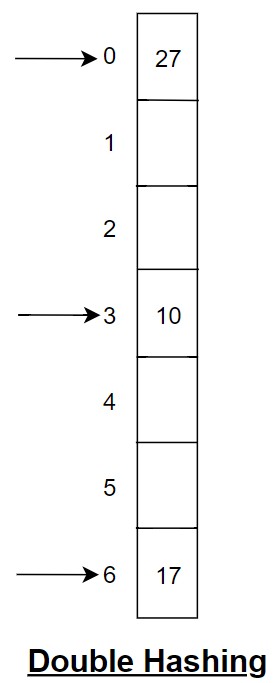
Example
Let m = 7 and Hash function h1(k) = k mod 7
h2(k) = i + 5 – (k mod 5) (i = 0 to m-1 & p = 5 less than m)
Insert key – 10, 17, 25
For 10,
10 mod 7 = 3 → index 3rd is empty → insert 10.
For 17,
17 mod 7 = 3 → collision → (h1(k) + (i*(h2(k)))) mod 7
Take i = 1,
This is equal to – (3 + (1* (5 – (17 mod 5))) mod 7 = (3 + 3) mod 7 = 6th index (empty) → insert 17.
For 27,
27 mod 7 = 6 → collision → (h1(k) + (i*(h2(k)))) mod 7
Take i = 1,
This is equal to – (3 + (1*(5 – (27 mod 5))) mod 7 = (3 + 3) mod 7 = 6th index (Full) → collision
Let’s take i = 2,
This is equal to – (3 + (2*(27 mod 5))) mod 7 = (3 + 4) mod 7 = 0th index (empty) → insert 27.
Table looks like –
Time Complexity – Double Hashing
- Best case – O(1)
- Average case – O(1)
- Worst case – O(n)
Among all open addressing methods, double hashing gives best distribution.
Space Complexity – Double Hashing
The space complexity of Double Hashing is O(m). There is no extra linked lists. It is only an array.
.
Comparison
Linear Probing
- Simple
- Suffers from primary clustering
Quadratic Probing
- Reduces primary clustering
- Still secondary clustering
Double Hashing
- Best distribution
- Least clustering
But all require α < 1. As α approaches 1, performance collapses.
.
Applications of Open Addressing
Open Addressing is used in
- Hash tables in embedded systems
- Memory-constrained environments
- Symbol tables in compilers
- High-performance in-memory caches
Test Yourself
Q1- In Quadratic Probing, a table of size m may fail to insert even if empty slots exist because
Load factor is zero
Probe sequence does not cover all slots
Hash function is perfect
Table size is even
Ans – (2)
Explanation – Quadratic probing does not always guarantee visiting all table slots. Some empty slots may never be reached depending on m and hash function.
Q2- In Double Hashing, if h2(k) = 0 for some key, what happens?
Perfect distribution
Infinite loop
Linear probing
No collision
Ans – (2)
Explanation – If step size becomes zero, probe sequence becomes constant index. It will repeatedly check same slot and never move.
Q3- For unsuccessful search in Linear Probing, expected time increases rapidly when
α is small
α is close to 0.5
α is close to 1
m is prime
Ans – (3)
Explanation – As α, the load factor = n/m approaches 1, long clusters form. Unsuccessful search scans almost entire cluster.
Q4- If m = 10 and we use h(k) = k mod 10 with Linear Probing, inserting 20, 30, 40, 50 will create
Even distribution
No collision
A growing cluster
Secondary clustering
Ans – (3)
Explanation – All hash to 0. They will occupy 0, 1, 2, 3 forming a cluster.
Q5- If deletion marks slot as empty instead of “deleted”, then
Performance improves
Searching may fail incorrectly
Clustering reduces
Table resizes
Ans – (2)
Explanation – If we mark slot empty, search may stop early and conclude key not present, even if it exists later in probe sequence.
Q6- In Open Addressing, maximum number of elements stored is
m
n
m-1 always
Infinite
Ans – (1)
Explanation – Since all elements stored in array, capacity is m.
Q7- If table size is not prime in Double Hashing, possible issue is
Faster insertion
Infinite probing cycle
Reduced memory
No issue
Ans – (2)
Explanation – If step size and table size share common factors, probe may cycle over subset of indices only.
Q8- Which case gives worst clustering behavior?
Linear Probing with α = 0.3
Linear Probing with α = 0.95
Double Hashing with α = 0.4
Quadratic Probing with α = 0.2
Ans – (2)
Explanation – Linear probing at very high load factor causes huge primary clusters.
Q9- Give a scenario where Quadratic Probing fails even when table has empty slots.
Ans – If m is not chosen properly (for example, not prime), quadratic increments may repeat before covering all slots. Some empty slots remain unreachable.
Q10- Explain difference between primary and secondary clustering.
Ans – Primary clustering occurs when consecutive slots form large blocks due to linear probing. Secondary clustering occurs when keys with same initial hash follow same probe sequence.
Q11- Why do practical systems resize table around α ≈ 0.7?
Ans – Because after that point, expected probe length starts increasing rapidly. Resizing keeps performance near constant time.